How Corporate Security Actually Works in Modern Businesses
HRS
Active Support
Around the clock protection

Today, corporate security is a proactive system to prevent problems from escalating into an operational disruption, a safety issue, or a reputational concern.
Corporate security works by identifying risk, controlling exposure, and protecting the people, assets, and operations that keep a business running
Businesses are far more complex than they were even ten years ago. Employees shift between physical and digital workspaces. Executives continue to be in the public eye. Sensitive information is in offices, labs, campuses, and meeting rooms. Buildings are traversed daily by visitors, vendors, contractors, and clients. A small incident can turn into an operational disruption, damage to reputation, or exposure to liability in no time.
Security for businesses exists to create structure, awareness, and control within that environment.
It’s not just a guard standing at a door. It’s a coordinated system of people, procedures, technology, intelligence, planning, and operational oversight aimed at stopping disruption before it happens.

Security for Businesses Starts With Risk Assessment
All successful corporate security programs begin with an understanding of risk.
Before placing personnel, access systems, or developing response procedures, a company must know what to protect and where the exposure is. This process is called a security assessment or vulnerability assessment.
The assessment measures the overall operating environment. It examines building design, employee movement, visitor flow, executive exposure, access points, neighborhood conditions, after-hours activity, emergency preparedness, and the overall risk profile of the organization.
A biotech facility in South San Francisco has different concerns than a venture capital office in Palo Alto or a technology startup in San Francisco. That’s why modern business protection is never one-size-fits-all.
The goal of the assessment is straightforward: find weaknesses before they turn into incidents.
Access Control: The Foundation of Security
One of the most important functions of corporate security is controlling access.
At its core, access control ensures that the right people can enter the right spaces while unauthorized individuals are prevented from gaining access to sensitive environments.
In modern workplaces, this often includes badge systems, biometric readers, visitor check-ins, restricted areas, executive floors, and after-hours access protocols. Businesses handling intellectual property, financial information, legal records, or research materials rely heavily on controlled environments to reduce exposure.
Access control is especially critical in high-density corporate environments such as multi-tenant office buildings, headquarters, technology campuses, and biotech facilities where large numbers of employees, visitors, vendors, and contractors move throughout the property every day.
Without access controls, companies lose visibility into who is entering the environment, why they are there, and where they can go once they get there.
Security Personnel and Physical Presence
Security for companies also works through trained personnel who provide a visible and operational layer of protection.
Modern security professionals do far more than simply observe and report. They are trained to monitor behavior, manage incidents, support workplace safety, de-escalate conflict, coordinate emergency response, document activity, and maintain situational awareness throughout the environment.
The presence itself plays an important role. A professional security presence creates deterrence, improves response time, and reassures employees and visitors that the environment is being actively managed.
In high-end corporate settings, security personnel must also reflect the professionalism of the organization they represent. They often operate within lobbies, headquarters, executive environments, campuses, parking structures, events, and sensitive facilities where communication skills and composure are just as important as physical readiness.
The strongest security presence is often the least disruptive. Good corporate security blends naturally into the environment while maintaining awareness and control at all times.
Workplace Safety and Incident Response
Business security also prepares organizations for incidents before they occur.
Today’s businesses face several operational and workplace concerns, including unauthorized access, suspicious behavior, workplace conflict, medical emergencies, public disturbances, employee safety issues, and emergency evacuations.
Without structure, small incidents can turn into chaos.
Corporate Security designs the processes for how incidents are identified, escalated, documented, and resolved. The employees know who to call, the leadership understands the decision-making process of what to respond to and how, and the security team coordinates the stabilization efforts in real-time.
Preparation = less confusion.
When organizations lack incident planning, response becomes reactive and inconsistent. Security programs create operational clarity during situations where clarity matters most.
Monitoring and Protective Intelligence
Today’s company security is more intelligence-led.
Instead of waiting for incidents to occur, organizations are now seeking to detect warning signs early enough to stop them from escalating. This is where monitoring and protective intelligence become relevant.
Protective intelligence is the analysis of a pattern, vulnerability, operational concern, or suspicious activity that may present a heightened risk. This could be something like monitoring physical activity around a building or scanning incident trends in some environments. In other cases, it might be about evaluating executive risk, identifying operational vulnerabilities, or spotting warning signs of potential disruption before it occurs.
In cases where a company is in the public eye or has visible leadership, security teams may also monitor for demonstrations, unwanted attention, online threats, or reputational concerns that could ultimately impact physical operations.
The sooner a risk is identified, the easier it is to manage it without impacting the business.
Executive Protection and Leadership Support
As companies scale, leaders and founders become more visible.
The leadership teams participate in investor meetings, conferences, media appearances, public events, negotiations, and sensitive internal meetings, which increase their overall exposure. Executives in the Bay Area, especially in the fields of technology, venture capital, biotech, and corporate leadership, often find themselves working in a very visible industry where the spotlight can create risk very quickly.
Corporate protection allows leadership to operate normally while minimizing unnecessary exposure.
Executive protection isn’t about putting on a show or being intimidating. It’s about planning movement, controlling access, maintaining situational awareness, and ensuring that executives can travel, meet, and operate without disruption.
It may involve planning, route coordination, discreet protective presence, event oversight, or secure transportation support, depending on the environment and risk profile involved.
It’s not visibility; it’s continuity and stability.
Corporate Security is Built Around Prevention
The biggest misconceptions about business security are that it only exists for the purpose of responding to emergencies.
The best security programs are, in fact, prevention-oriented.
“Most major incidents start as small problems that were ignored, overlooked, or not managed.” An unauthorized visitor, an unsecured entry point, unusual behavior, poor communication, or a lack of operational structure can provide opportunities for larger disruption later.
The way business protection works is to break the escalation early.
“Visible deterrence, controlled access, trained personnel, operational awareness, and rapid communication all work together to reduce exposure before incidents become serious problems.”
Modern corporate security is different from traditional guard coverage in that it is preventive.
Corporate Protection Supports Daily Operations
Corporate protection is not separate from the business. It’s a part of it.
The most effective security programs are embedded in daily operations by supporting leadership, employees, facilities teams, human resources, IT departments, and executive administration.
Security helps keep things running more smoothly by boosting confidence in the workplace, structuring access procedures, minimizing ambiguity during incidents, and ensuring continuity in the face of disruptions.
Employees travel to and from the office more safely. Visitors are able to traverse the environment more efficiently. Executives are more upbeat. Incidents are well documented and are resolved faster.
When security is done right, it doesn’t create friction. It takes it away.
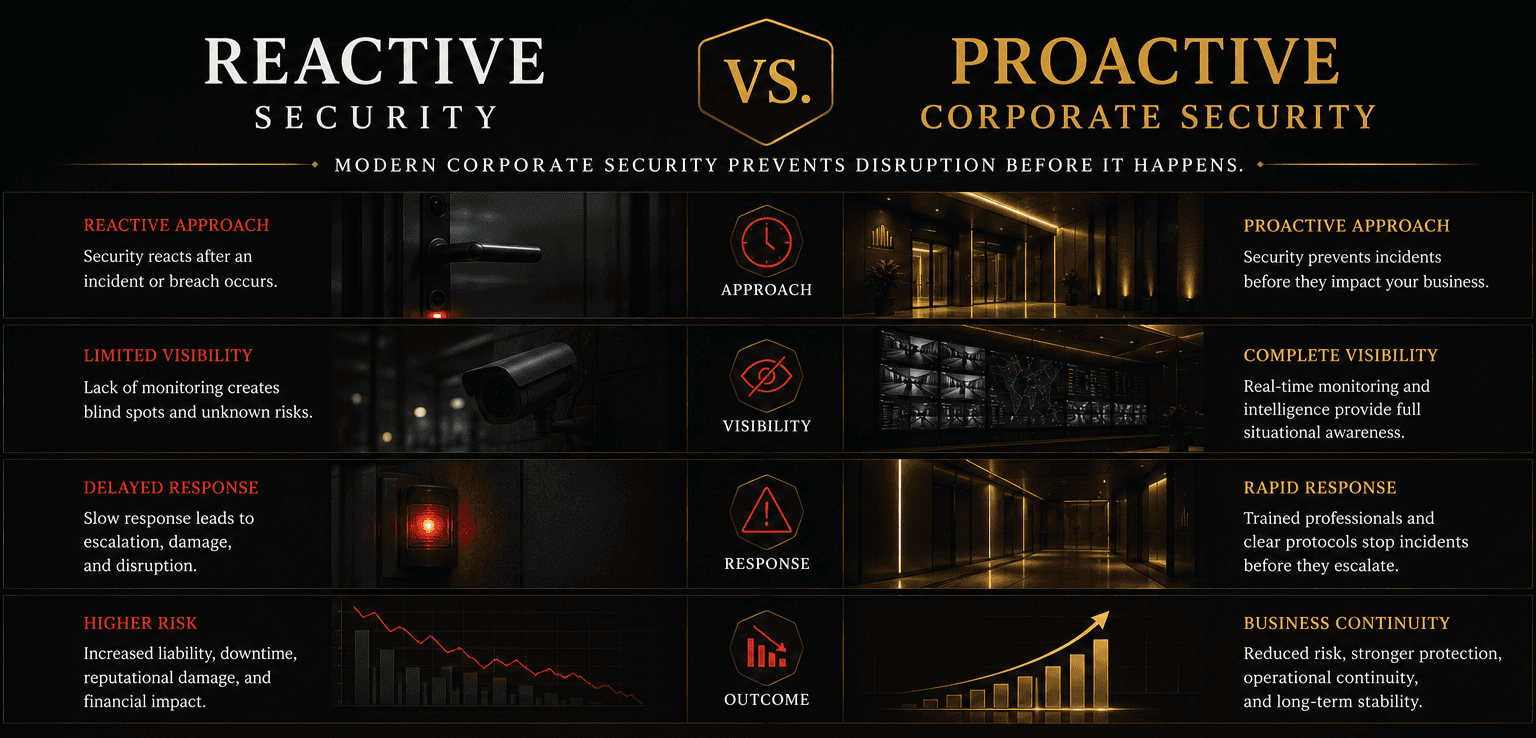
Reactive Security vs. Proactive Security
Traditional security models were fundamentally reactive. That’s not how corporate security works today.
Modern programs look for vulnerabilities before an incident happens; they don't wait for disruption. They blend planning, intelligence, operational awareness, and structured procedures into a layered system that tries to reduce exposure proactively.
This is one of the biggest reasons why companies are rethinking how security works today.
Organizations are no longer content to sit back. They need operational support, continuity, awareness, and prevention.
How Business Security Works in the Bay Area
The Bay Area also has unique operational challenges, as many businesses operate in dense urban environments, public-facing headquarters, innovation hubs, multi-tenant office towers, biotech corridors, and high-traffic districts.
A San Francisco company may be managing executive visibility, workplace safety concerns, intellectual property protection, employee movement, and operational continuity all at the same time, as may an Oakland company, a Palo Alto company, a Menlo Park company, a San Jose company, and a South San Francisco company.
That means security programs have to be tailored and customized to the real environment.
A startup office in SoMa doesn’t demand the same posture as a biotech campus in South San Francisco or a corporate headquarters in downtown San Jose. Good corporate security does not adopt a generic coverage approach and apply it everywhere. Rather, it is customized to the organization’s specific operational realities.
Corporate Protection Is a Layered System
One guard, one camera, or one badge system cannot protect a business.
Corporate security works because many layers work together at the same time. Resiliency is built through the interaction of personnel, technology, planning, communication, procedures, monitoring, and operational oversight.
If one layer fails, another lessens exposure before the problem worsens.
That layered approach is what allows businesses to be stable even in unpredictable environments.
Final Takeaway
Corporate security supports businesses to manage risk before disruption occurs.
It integrates physical presence, access control, workplace safety, operations planning, protective intelligence, and executive support into one coordinated system to protect people, assets, leadership, and continuity.
Fear is not the goal. Stability is the aim.
Because modern business moves fast, happens in public, and is always exposed. Business security exists to keep them running safely, confidently, and without unnecessary disruption.


We have used Veterans Covert Protection Group for our biggest event and nightly security. They are the FANTASTIC!!! The level of professionalism goes above and beyond. They were involved with every step of the process and made us feel like we were in great hands from our first interaction. I would highly recommend you hire them if you or your business has any security needs. They are 10/5 stars!!!!
Erin M
Pleasanton, CA
Reviews
Service Locations
Office
5674 Stonerdige Dr Pleasanton, CA 94588 United States
VCPG Trusted by the
Best in the Industry

































